Last updated on May 12, 2022
An Introduction to Tailgating Attacks
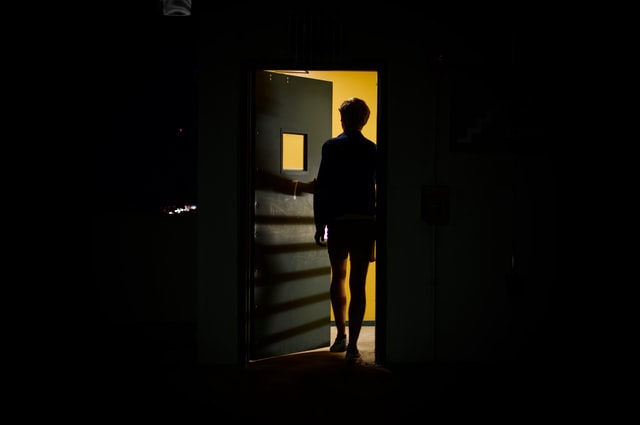
A social engineering attack that features more of a physical element than a virtual one is known as a “Tailgating attack“. In essence, tailgating is a social engineering attack where the attacker follows an authorized person into a restricted area in which they are not permitted to be. When thinking about data breaches, people often think about shady cybercriminals operating from a distant location. However, letting someone without legitimate access enter your premises – potentially through a tailgating attack – actually pose real a risk for organizations to leak private or sensitive information.
How? Let’s find out.
What is a Tailgating Attack in Social Engineering?
A so-called tailgating attack could be used to gain access to a restricted area by manipulating for instance a delivery person, a repairman, or virtually anyone that can provide access to the restricted area. The simplest and most effective way to trick people is to enter a section they aren’t authorized to enter as they open the door.
Tailgating Attack Examples
Here are a few examples of tailgating social engineering attacks.
1. Walk behind employees as they open doors
Employees opening doors to restricted areas are monitored by social engineers. Leaving a door open for people behind us is common sense, so this is what we do. A nonauthorized attacker seeking entry with malicious intentions may unknowingly gain physical access due to the negligence of an employee.
2. Pose as a courier or delivery driver
As couriers and delivery personnel, buildings can be breached by social engineers and circulate freely within them. Depending on how well they probe, a receptionist or employee may also allow them access to a floor/office they claim to have a delivery at.
3. Pretend their hands are too full to open doors
Similarly, social engineers can gain access to the office by bringing multiple items with them as they walk to the door. Similarly to when they leave a door open behind them, employees can open a door for an intruder as a gesture of courtesy and kindness.
4. Claim to have ‘forgotten their ID’
It is possible to mark yourself as an employee with conviction by claiming that you have lost your access ID or leaving it at home. By doing so, they were hoping some kind person would open a door for them, or give them a temporary pass.
5. Tailgating using Thermal Imaging
In the video below, a more advanced high-tech example is demonstrated. If you are serious about your security, you might want to consider this approach, even if it’s very unusual.
How to Prevent Tailgating Attacks in Social Engineering
Many people believe that a tailgating social engineering attack can be hard to avoid since it requires them to separate themselves from some social norms. Nevertheless, some of the security measures described in the next section can help avoid this kind of attack.
Training
You should train your employees to avoid tailgating attack as the first step. It is important for them to be aware of the negative consequences of tailgating. As a result, employees should observe their environment and report malicious activity when it occurs.
Smart cards and badges
Businesses with large offices are often the targets of tailgating attacks. Companies with several floors typically employ many people. Therefore, people do not always know who works in the building. For verification purposes, a badge or smart card will be needed to verify your employees’ identities.
Visitor’s badge
You’ll also need badges for visitors, just like you do for employees. Your employees are impersonated by imposters who have made their way into the building. Therefore, they are indistinguishable. Nonetheless, a badge will show visitors that they cannot access all areas, so you can identify them as visitors.
Biometrics and electronic access control
Technology can help you everywhere in your life. You can prevent social engineering attacks like tailgating by implementing biometrics and other electronic access control in your organization. Biometric verifications are the best way to ensure that those who are allowed into the restricted areas are properly authorized. As a result, only authorized personnel are allowed into the restricted areas.
Be First to Comment